modifying the settings on the local OAuth server that control how long tokens are valid by default
OpenShift's OAuth server (OpenShift Container Platform)
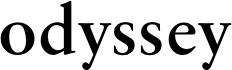
An OAuth Configuration server is preconfigured and ready to go on the OpenShift Container Platform master node. Users are required to acquire OAuth access tokens before they can authenticate themselves with the API and use it successfully.
When a new OAuth token is requested, the OAuth server will inquire with the identity provider that has been chosen in order to determine the user who is making the request and their credentials. This gives the server the ability to decide whether to allow the user access to the resource or not.
After that, it determines which user that identity is associated with, then it generates an access token for that user, and finally, it returns the token so that it can be utilized.
The procedure of making OAuth token requests and responding to those requests.
Both the conventional OAuth authorization code grant and the implicit grant OAuth authorization flow are supported by the OAuth server. The regular OAuth authorization code grant is the more common type.
Also included is information regarding how these responses should be handled. 401 Invalid or Unauthorized 401 Invalid or Unauthorized
The action that the OAuth server takes is determined by the client to which the token requests were sent.
The following is a list of some of the default ways that you could utilize:
Collect data that is particular to the response times of the network, the front-end, and the back-end.
Acquire a grasp of how different geographies, browsers, device types, and Internet service providers affect the performance of your website.
Among other things, obtain fresh perspectives on web transactions, user sessions, AJAX calls, and Javascript problems.
Keep an eye on how long it takes for websites to respond using first-party, third-party, and content delivery network (CDN) networks.
Content Analysis and Monitoring on Websites
Crawl the website and monitor it automatically for any changes to the content in order to prevent any unauthorized changes to the website or its defacement. This contributes to the process of ensuring that the data hosted on your websites is accurate. You have the ability to set up alarms that will cause you to take prompt action in the event that any unauthorized modifications are made to the content of your website, and there are choices that provide you the ability to restore the material to its prior state. When you use Applications Manager's website monitor, you will be able to examine the totality of the website in search of issues related to the page's content quality as well as conduct a search for links that have been compromised.

 women in street dancing
Photo by
women in street dancing
Photo by  man and woman standing in front of louver door
Photo by
man and woman standing in front of louver door
Photo by  man in black t-shirt holding coca cola bottle
Photo by
man in black t-shirt holding coca cola bottle
Photo by  red and white coca cola signage
Photo by
red and white coca cola signage
Photo by  man holding luggage photo
Photo by
man holding luggage photo
Photo by  topless boy in blue denim jeans riding red bicycle during daytime
Photo by
topless boy in blue denim jeans riding red bicycle during daytime
Photo by  trust spelled with wooden letter blocks on a table
Photo by
trust spelled with wooden letter blocks on a table
Photo by  Everyone is Welcome signage
Photo by
Everyone is Welcome signage
Photo by  man with cap and background with red and pink wall l
Photo by
man with cap and background with red and pink wall l
Photo by  difficult roads lead to beautiful destinations desk decor
Photo by
difficult roads lead to beautiful destinations desk decor
Photo by  photography of woman pointing her finger near an man
Photo by
photography of woman pointing her finger near an man
Photo by  closeup photography of woman smiling
Photo by
closeup photography of woman smiling
Photo by  a man doing a trick on a skateboard
Photo by
a man doing a trick on a skateboard
Photo by  two men
two men  running man on bridge
Photo by
running man on bridge
Photo by  orange white and black bag
Photo by
orange white and black bag
Photo by  girl sitting on gray rocks
Photo by
girl sitting on gray rocks
Photo by  assorted-color painted wall with painting materials
Photo by
assorted-color painted wall with painting materials
Photo by  three women sitting on brown wooden bench
Photo by
three women sitting on brown wooden bench
Photo by 
 Photo by
Photo by  Photo by
Photo by  Photo by
Photo by  Photo by
Photo by 
 people sitting on chair in front of computer
people sitting on chair in front of computer

 all stars lol GIF by Lifetime
all stars lol GIF by Lifetime two women talking while looking at laptop computerPhoto by
two women talking while looking at laptop computerPhoto by  shallow focus photography of two boys doing wacky facesPhoto by
shallow focus photography of two boys doing wacky facesPhoto by  happy birthday balloons with happy birthday textPhoto by
happy birthday balloons with happy birthday textPhoto by  itty-bitty living space." | The Genie shows Aladdin how… | Flickr
itty-bitty living space." | The Genie shows Aladdin how… | Flickr shallow focus photography of dog and catPhoto by
shallow focus photography of dog and catPhoto by  yellow Volkswagen van on roadPhoto by
yellow Volkswagen van on roadPhoto by  orange i have a crush on you neon light signagePhoto by
orange i have a crush on you neon light signagePhoto by  5 Tattoos Artist That Will Make You Want A Tattoo
5 Tattoos Artist That Will Make You Want A Tattoo woman biting pencil while sitting on chair in front of computer during daytimePhoto by
woman biting pencil while sitting on chair in front of computer during daytimePhoto by  a scrabbled wooden block spelling the word prizePhoto by
a scrabbled wooden block spelling the word prizePhoto by 
 StableDiffusion
StableDiffusion
 StableDiffusion
StableDiffusion
 StableDiffusion
StableDiffusion





