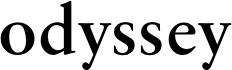
In order to use an OAuth Provider to authenticate your app, a sequence of configuration actions must be completed by several roles (Site Administrator, Business Administrator, API Provider, and App Developer).
An overview OAuth Configuration of the general process and roles involved in each job is provided as part of this quick start.
The OAuth 2.0 Provider Service Configuration
- Right-click on the Add a Service button in the AM console and select Realms.
- Finally, press the Create button without filling out any other fields.
- There is an OAuth 2.0 provider page on the site.
The following is further information:
The UMA's Grant Flow
Configure your environment's Response Type Plugins in accordance with the grant type flows you permit. Tokenization plugins allow the provider to issue access tokens, ID tokens and other types of tokens.
With the id token and none response types in place, OpenID Connect processes can use either of these methods.
- The grant of an authorisation code makes use of the code response type.
- The response type device code is utilised in the device grant flow.
- In order to issue access and refresh tokens, the token response type is needed by all flows.
- (Optional) Please refer to the "Additional Configuration" section for additional options.
Additions to the Settings
Changing the attribute used to retrieve a user's profile in OAuth 2.0
AM authentication must be configured for external identity repositories where users log in using their e-mail address or other profile characteristic instead of their username.
Use the following steps, for example, to set up AM such that OAuth 2.0 resource owners can log in with their email addresses stored in the LDAP profile attribute mail:
OAuth2 provider Advanced tab: Add LDAP profile attribute to User Profile Attribute(s) Resource Owner is Authenticated On list, then save your modifications.
Go to the Authentication Configuration page in Realm Name > Identity Stores > Identity Store Name.
Set the required LDAP property in the Authentication Naming Attribute box. For instance, you can send a letter.
Use an LDAP authentication module or an LDAP decision node to connect the identity repository to the LDAP directory service.
Create the following values in the following fields in both scenarios:
Select mail as the attribute in the Attribute Used to Retrieve User Profile area.
Make sure you save your modifications before exiting the application.
Ensuring that the resource owners utilise the LDAP module or node where you have configured the authentication tree or chain is essential.
REST request for a specific access token.
Configure the auth chain setting.
Overrides the realm-level setting below for each realm.
Set the Password Grant Authentication Service property in the Realms > Realm Name > OAuth2 Provider > Advanced.
Dedicated to a specific area.
For example, go to the realm name, authentication, settings, and select the core option for organisation authentication configuration, as shown below.
For everyone and everything.
Go to Configuration > Core Attributes>Core, and set the Organization Authentication Configuration property there.

 women in street dancing
Photo by
women in street dancing
Photo by  man and woman standing in front of louver door
Photo by
man and woman standing in front of louver door
Photo by  man in black t-shirt holding coca cola bottle
Photo by
man in black t-shirt holding coca cola bottle
Photo by  red and white coca cola signage
Photo by
red and white coca cola signage
Photo by  man holding luggage photo
Photo by
man holding luggage photo
Photo by  topless boy in blue denim jeans riding red bicycle during daytime
Photo by
topless boy in blue denim jeans riding red bicycle during daytime
Photo by  trust spelled with wooden letter blocks on a table
Photo by
trust spelled with wooden letter blocks on a table
Photo by  Everyone is Welcome signage
Photo by
Everyone is Welcome signage
Photo by  man with cap and background with red and pink wall l
Photo by
man with cap and background with red and pink wall l
Photo by  difficult roads lead to beautiful destinations desk decor
Photo by
difficult roads lead to beautiful destinations desk decor
Photo by  photography of woman pointing her finger near an man
Photo by
photography of woman pointing her finger near an man
Photo by  closeup photography of woman smiling
Photo by
closeup photography of woman smiling
Photo by  a man doing a trick on a skateboard
Photo by
a man doing a trick on a skateboard
Photo by  two men
two men  running man on bridge
Photo by
running man on bridge
Photo by  orange white and black bag
Photo by
orange white and black bag
Photo by  girl sitting on gray rocks
Photo by
girl sitting on gray rocks
Photo by  assorted-color painted wall with painting materials
Photo by
assorted-color painted wall with painting materials
Photo by  three women sitting on brown wooden bench
Photo by
three women sitting on brown wooden bench
Photo by 
 Photo by
Photo by  Photo by
Photo by  Photo by
Photo by  Photo by
Photo by 
 people sitting on chair in front of computer
people sitting on chair in front of computer

 all stars lol GIF by Lifetime
all stars lol GIF by Lifetime two women talking while looking at laptop computerPhoto by
two women talking while looking at laptop computerPhoto by  shallow focus photography of two boys doing wacky facesPhoto by
shallow focus photography of two boys doing wacky facesPhoto by  happy birthday balloons with happy birthday textPhoto by
happy birthday balloons with happy birthday textPhoto by  itty-bitty living space." | The Genie shows Aladdin how… | Flickr
itty-bitty living space." | The Genie shows Aladdin how… | Flickr shallow focus photography of dog and catPhoto by
shallow focus photography of dog and catPhoto by  yellow Volkswagen van on roadPhoto by
yellow Volkswagen van on roadPhoto by  orange i have a crush on you neon light signagePhoto by
orange i have a crush on you neon light signagePhoto by  5 Tattoos Artist That Will Make You Want A Tattoo
5 Tattoos Artist That Will Make You Want A Tattoo woman biting pencil while sitting on chair in front of computer during daytimePhoto by
woman biting pencil while sitting on chair in front of computer during daytimePhoto by  a scrabbled wooden block spelling the word prizePhoto by
a scrabbled wooden block spelling the word prizePhoto by 
 StableDiffusion
StableDiffusion
 StableDiffusion
StableDiffusion
 StableDiffusion
StableDiffusion





